Hi all 
I'm starting my adventure with Elstick and please be patient to Me 
I have such a case.I would like to know if there is anything to be afraid of 
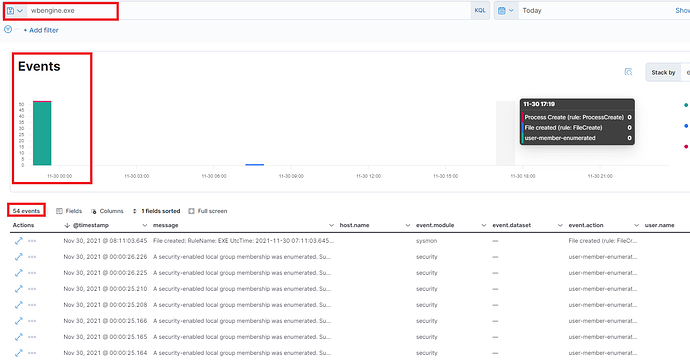
I got the message from Elastick: "A security-enabled local group membership was enumerated" -> It's about -> wbengine.exe file. This occurs on one of my server.
The question is how can i know if it's a normal behavior or not.
I would like to ask for valuable tips and any help from Your site 
Message: "A security-enabled local group membership was enumerated. Subject: Security ID: S-1-5-18 Account Name: XXX Account Domain: XYZ
Logon ID: 0x3E7 Group: Security ID: S-1-5-32-544 Group Name: Administrators Group Domain: Builtin Process Information: Process ID: 0x36fc Process Name: C:\Windows\System32\wbengine.exe"
{
"_id": "ItSub30BacWe7FLt0Nqi",
"_index": "winlogbeat-7.15.1-2021.11.02-000001",
"_score": "1",
"_type": "_doc",
"@timestamp": "2021-11-30T07:11:03.645Z",
"agent": {
"ephemeral_id": "a9caa39c-b776-4ba6-91e3-6d5fe2dc8338",
"hostname": "XXX",
"id": "98d9d801-45cc-4386-aa2f-d2285ab46ba1",
"name": "XXX",
"type": "winlogbeat",
"version": "7.15.1"
},
"ecs": {
"version": "1.11.0"
},
"event": {
"action": "File created (rule: FileCreate)",
"category": "file",
"code": "11",
"created": "2021-11-30T07:11:05.334Z",
"kind": "event",
"module": "sysmon",
"provider": "Microsoft-Windows-Sysmon",
"type": "creation"
},
"file": {
"directory": "C:\Users\XYZ\Desktop",
"extension": "exe",
"name": "wbengine.exe",
"path": "C:\Users\XYZ\Desktop\wbengine.exe"
},
"host": {
"architecture": "x86_64",
"hostname": "XXX",
"id": "fab3cb5d-0876-4a2e-a797-830b010ca60d",
"ip": "fe80::f103:8015:ed95:7ec5,10.255.200.24",
"mac": "00:15:5d:c8:06:22",
"name": "XYZ",
"os": {
"build": "17763.1879",
"family": "windows",
"kernel": "10.0.17763.1879 (WinBuild.160101.0800)",
"name": "Windows Server 2019 Standard",
"platform": "windows",
"type": "windows",
"version": "10.0"
}
},
"log": {
"level": "information"
},
"message": "File created:\nRuleName: EXE\nUtcTime: 2021-11-30 07:11:03.645\nProcessGuid: {fab3cb5d-c60d-61a5-69fe-030000000500}\nProcessId: 12752\nImage: C:\WINDOWS\Explorer.EXE\nTargetFilename: C:\Users\XYZ\Desktop\wbengine.exe\nCreationUtcTime: 2021-11-30 07:11:03.645\nUser: XYZ",
"process": {
"entity_id": "{fab3cb5d-c60d-61a5-69fe-030000000500}",
"executable": "C:\WINDOWS\Explorer.EXE",
"name": "Explorer.EXE",
"pid": "12752"
},
"rule": {
"name": "EXE"
},
"winlog": {
"api": "wineventlog",
"channel": "Microsoft-Windows-Sysmon/Operational",
"computer_name": "XYZ",
"event_data": {
"CreationUtcTime": "2021-11-30 07:11:03.645",
"User": "XXX"
},
"event_id": "11",
"opcode": "Info",
"process": {
"pid": "11832",
"thread": {
"id": "276"
}
},
"provider_guid": "{5770385f-c22a-43e0-bf4c-06f5698ffbd9}",
"provider_name": "Microsoft-Windows-Sysmon",
"record_id": "18565",
"task": "File created (rule: FileCreate)",
"user": {
"domain": "NT AUTHORITY",
"identifier": "S-1-5-18",
"name": "SYSTEM",
"type": "User"
},
"version": "2"
}
}
BR,
Luk