This is a really interesting issue.
Code related: elastic-agent/client.go at cda5b7e75d080c6be9e9220dfa607c145cf598b4 · elastic/elastic-agent · GitHub
I've using self-signed CA to deploy elastic-agent in internal environment, enrolling *nix agent works perfect cuz I've previously trusted all CAs in local machine.
However, when it comes to Windows 10 / Windows Server 2022, things got changed.
Use the https --url and --enrollment-token with install subcommand of elastic-agent on Windows Server 2022, I got this in DEBUG level logging:
{"log.level":"info","@timestamp":"2023-05-30T23:08:34.717+0800","log.origin":{"file.name":"cmd/enroll_cmd.go","file.line":475},"message":"Starting enrollment to URL: https://MY-DOMAIN:8220/","ecs.version":"1.6.0"}
{"log.level":"debug","@timestamp":"2023-05-30T23:08:34.948+0800","log.origin":{"file.name":"remote/client.go","file.line":172},"message":"Request method: POST, path: /api/fleet/agents/enroll, reqID: 01H1PK8A84J9XTADNJ7YG95R5C","ecs.version":"1.6.0"}
{"log.level":"debug","@timestamp":"2023-05-30T23:08:34.949+0800","log.origin":{"file.name":"remote/client.go","file.line":186},"message":"Creating new request to request URL https://MY-DOMAIN:8220/api/fleet/agents/enroll?","ecs.version":"1.6.0"}
{"log.level":"debug","@timestamp":"2023-05-30T23:08:34.960+0800","log.origin":{"file.name":"remote/client.go","file.line":220},"message":"requester 0/1 to host https://MY-DOMAIN:8220/ errored","error":{"message":"Post \"https://MY-DOMAIN:8220/api/fleet/agents/enroll?\": remote error: tls: access denied"},"ecs.version":"1.6.0"}
Error: fail to enroll: fail to execute request to fleet-server: remote error: tls: access denied
So the elastic-agent failed to get installed.
Chrome can access 8220 port (/api/status returned HEALTHY) without any error.
Then I captured traffic using wireshark, things start to get interesting now:
Chrome requesting HTTPS /api/status , working fine:
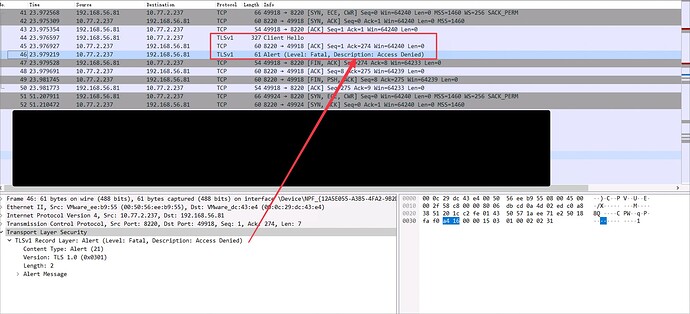
Elastic-Agent Enroll, failed immediately even before Server Hello:
Comparing ClientHello and Server supported TLS protocol, seems all good:
Left-one is client-hello, right-one is server-hello, so this comparison should result in no issue.
So there must be something wrong and a bug might be here.
BTW, I've confirmed that there is NO PROXY set in the environment.
After analyzing your golang code, I found it just a wrapper of http.Client and write a request client myself like this:
package main
import (
"fmt"
"io"
"bytes"
"net/http"
)
func main() {
url := "https://MY-DOMAIN:8220/api/fleet/agents/enroll"
data := `{"a": 1}`
req, err := http.NewRequest("POST", url, bytes.NewBufferString(data))
if err != nil {
fmt.Println("Error creating request:", err)
return
}
client := &http.Client{}
resp, err := client.Do(req)
if err != nil {
panic(err)
return
}
defer resp.Body.Close()
body, err := io.ReadAll(resp.Body)
if err != nil {
fmt.Println("Error reading response body:", err)
return
}
fmt.Println("Response body:", string(body))
}
which works like a charm, and give the HTTP 200 as expected. So there should be no issue on the server side. Also, I do not enable mTLS authentication, only token and password will be used for auth.