Dear Team,
I have ELK version - 6.3.1 and installed xpack trial version to check rules and privileges for normal user and admin user.
So I have created an user (user1) with only one indices aliases(event_aliases01), when i tried to login with user1 , i can able to login successfully, but the problem is , when i go Discover section and i choose the index pattern(It is an aliases) and getting below error in the top of the kibana dashboard,
original index name : events_prabhu
Aliases name : event_aliases01
Kibana Index pattern name : event_aliases01
Discover: Failed to derive xcontent
Error: Request to Elasticsearch failed: {"error":{"root_cause":[{"type":"x_content_parse_exception","reason":"Failed to derive xcontent"}],"type":"search_phase_execution_exception","reason":"all shards failed","phase":"query","grouped":true,"failed_shards":[{"shard":0,"index":"events_prabhu","node":"Auqfigf2SWWqVVWjWPcjGQ","reason":{"type":"x_content_parse_exception","reason":"Failed to derive xcontent"}}],"caused_by":{"type":"x_content_parse_exception","reason":"Failed to derive xcontent","caused_by":{"type":"x_content_parse_exception","reason":"Failed to derive xcontent"}}},"status":400}
at http://192.168.4.89:5601/bundles/commons.bundle.js:204:84412
at Function.Promise.try (http://192.168.4.89:5601/bundles/commons.bundle.js:3:897645)
at http://192.168.4.89:5601/bundles/commons.bundle.js:3:897016
at Array.map ()
at Function.Promise.map (http://192.168.4.89:5601/bundles/commons.bundle.js:3:896974)
at callResponseHandlers (http://192.168.4.89:5601/bundles/commons.bundle.js:204:83771)
at http://192.168.4.89:5601/bundles/commons.bundle.js:204:69749
at processQueue (http://192.168.4.89:5601/bundles/vendors.bundle.js:211:199684)
at http://192.168.4.89:5601/bundles/vendors.bundle.js:211:200647
at Scope.$digest (http://192.168.4.89:5601/bundles/vendors.bundle.js:211:210409)
at http://192.168.4.89:5601/bundles/vendors.bundle.js:211:212941
at completeOutstandingRequest (http://192.168.4.89:5601/bundles/vendors.bundle.js:211:64424)
at http://192.168.4.89:5601/bundles/vendors.bundle.js:211:67265
So when i checked from Elasticsearch error logs i have got below messages,
[2018-12-17T20:07:05,313][DEBUG][o.e.a.s.TransportSearchAction] [Auqfigf] [events_prabhu][1], node[Auqfigf2SWWqVVWjWPcjGQ], [P], s[STARTED], a[id=usM6SkFYSbCPeDLZpXh_qA]: Failed to execute [SearchRequest{searchType=QUERY_THEN_FETCH, indices=[event_aliases01], indicesOptions=IndicesOptions[ignore_unavailable=true, allow_no_indices=true, expand_wildcards_open=true, expand_wildcards_closed=false, allow_aliases_to_multiple_indices=true, forbid_closed_indices=true, ignore_aliases=false], types=, routing='null', preference='1545057408841', requestCache=false, scroll=null, maxConcurrentShardRequests=5, batchedReduceSize=512, preFilterShardSize=64, allowPartialSearchResults=true, source={"size":500,"query":{"bool":{"must":[{"match_all":{"boost":1.0}},{"range":{"@timestamp":{"from":1545056525241,"to":1545057425241,"include_lower":true,"include_upper":true,"format":"epoch_millis","boost":1.0}}}],"adjust_pure_negative":true,"boost":1.0}},"version":true,"_source":{"includes":,"excludes":},"stored_fields":"","docvalue_fields":[{"field":"@timestamp","format":"date_time"},{"field":"enteredDate","format":"date_time"}],"script_fields":{},"sort":[{"@timestamp":{"order":"desc","unmapped_type":"boolean"}}],"aggregations":{"2":{"date_histogram":{"field":"@timestamp","time_zone":"Asia/Kolkata","interval":"30s","offset":0,"order":{"_key":"asc"},"keyed":false,"min_doc_count":1}}},"highlight":{"pre_tags":["@kibana-highlighted-field@"],"post_tags":["@/kibana-highlighted-field@"],"fragment_size":2147483647,"fields":{"":{}}}}}] lastShard [true]
org.elasticsearch.transport.RemoteTransportException: [Auqfigf][172.17.0.1:9300][indices:data/read/search[phase/query]]
Caused by: org.elasticsearch.common.xcontent.XContentParseException: Failed to derive xcontent
at org.elasticsearch.common.xcontent.XContentFactory.xContent(XContentFactory.java:191) ~[elasticsearch-x-content-6.4.2.jar:6.4.2]
at org.elasticsearch.xpack.core.security.authz.accesscontrol.SecurityIndexSearcherWrapper.evaluateTemplate(SecurityIndexSearcherWrapper.java:262) ~[?:?]
at org.elasticsearch.xpack.core.security.authz.accesscontrol.SecurityIndexSearcherWrapper.wrap(SecurityIndexSearcherWrapper.java:135) ~[?:?]
at org.elasticsearch.index.shard.IndexSearcherWrapper.wrap(IndexSearcherWrapper.java:76) ~[elasticsearch-6.4.2.jar:6.4.2]
at org.elasticsearch.index.shard.IndexShard.acquireSearcher(IndexShard.java:1199) ~[elasticsearch-6.4.2.jar:6.4.2]
at org.elasticsearch.index.shard.IndexShard.acquireSearcher(IndexShard.java:1190) ~[elasticsearch-6.4.2.jar:6.4.2]
at org.elasticsearch.search.SearchService.createSearchContext(SearchService.java:616) ~[elasticsearch-6.4.2.jar:6.4.2
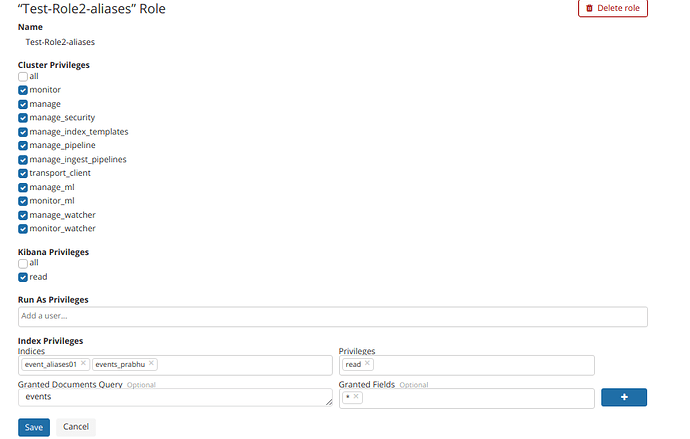
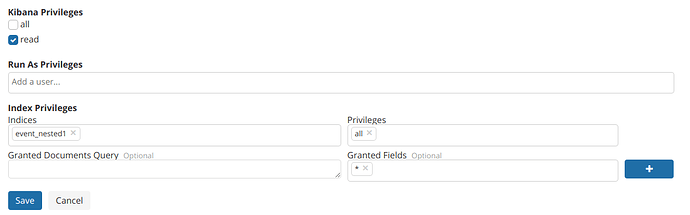
Below is my xpack user privileges details,
Could you please help me to fix this issue.