cat pipelines.yml
- pipeline.id: alpr
path.config: "/opt/bitnami/logstash/config/alpr.conf"
- pipeline.id: f5afm
path.config: "/opt/bitnami/logstash/config/f5afm.conf"
- pipeline.id: f5asm
path.config: "/opt/bitnami/logstash/config/f5asm.conf"
- pipeline.id: f5bot
path.config: "/opt/bitnami/logstash/config/f5bot.conf"
- pipeline.id: ingress
path.config: "/opt/bitnami/logstash/config/ingress.conf"
- pipeline.id: logstashrsyslog
path.config: "/opt/bitnami/logstash/config/logstashrsyslog.conf"
- pipeline.id: fortifw
path.config: "/opt/bitnami/logstash/config/fortifw.conf"
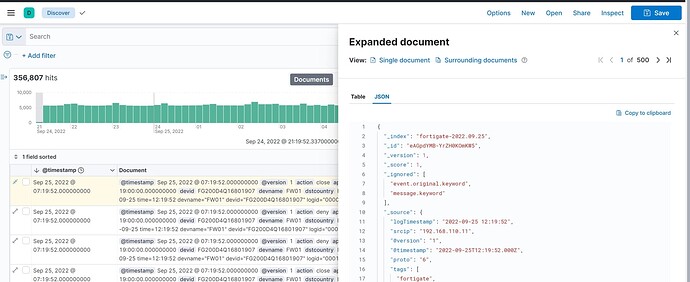
Wrong TIMESTAMP
input {
udp {
port => 9904
type => syslog
id => fortigate_9904
tags => ["fortigate","9904"]
}
}
filter {
if "fortigate" in [tags] {
mutate {
add_field => { "[@metadata][index]" => "fortigate-%{+YYYY.MM.dd}" }
add_tag => ["fortigate"]
add_field => [ "forti_host", "fw.mcfeetershq.local" ]
}
grok {
match => ["message", "%{SYSLOG5424PRI:syslog_index}%{GREEDYDATA:message}"]
overwrite => [ "message" ]
tag_on_failure => [ "failure_grok_fortigate" ]
}
kv { }
if [msg] {
mutate {
replace => [ "message", "%{msg}" ]
}
}
if [totalsession] {
mutate {
convert => { "totalsession" => "integer" }
}
}
if [cpu] {
mutate {
convert => { "cpu" => "integer" }
}
}
if [mem] {
mutate {
convert => { "mem" => "integer" }
}
}
if [setuprate] {
mutate {
convert => { "setuprate" => "integer" }
}
}
mutate {
add_field => ["logTimestamp", "%{date} %{time}"]
add_field => ["loglevel", "%{level}"]
replace => [ "fortigate_type", "%{type}"]
replace => [ "fortigate_subtype", "%{subtype}"]
remove_field => [ "msg", "type", "level", "date", "time" ]
}
date {
locale => "en"
match => ["logTimestamp", "YYYY-MM-dd HH:mm:ss"]
remove_field => ["logTimestamp", "year", "month", "day", "time", "date"]
add_field => ["type", "syslog"]
}
}
}
output {
elasticsearch {
hosts => ["https://mhqelastic-es-http:9200"]
index => "%{[@metadata][index]}"
user => "elastic"
password => "${ELASTICSEARCH_PASSWORD}"
ssl => true
cacert => "/var/data/tls.crt"
}
}
Correct Timestamp
input {
syslog {
port => 5344
tags => ["bot","5344"]
type => bot
id => "bot_syslog_listener_5344"
}
}
filter {
if [type] == 'bot' {
mutate { add_field => { "[@metadata][index]" => "bot-%{+YYYY.MM.dd}" } }
# grok {
# match => ["message", 'hostname=%{QS},bigip_mgmt_ip=%{QS},(bigip_mgmt_ip2=%{QS})?,client_ip=%{QS},client_ip_geo_location="N%{URIPATHPARAM}",client_port=%{QS},client_request_uri=%{QS},configuration_date_time="%{CISCOTIMESTAMP}",context_name=%{QS},context_type=%{QS},dest_ip=%{QS},dest_port=%{QS},device_product=%{QS},device_vendor=%{QS},device_version=%{QS},errdefs_msgno=%{QS},http_method=%{QS},http_protocol_indication=%{QS},http_protocol_info=%{QS},route_domain=%{QS},timestamp=%{QS},virtual_server_name=%{QS},device_id=%{QS},host=%{QS},request_date_time="%{CISCOTIMESTAMP}",profile_name=%{QS},support_id=%{QS},request_status=%{QS},action=%{QS},reason=%{QS},previous_action=%{QS},previous_support_id=%{QS},previous_request_date_time=%{QS},bot_signature=%{QS},bot_signature_category=%{QS},bot_name=%{QS},session_id=%{QS},class=%{QS},anomaly_categories=%{QS},anomalies=%{QS},additional_bot_signatures=%{QS},micro_service_name=%{QS},micro_service_type=%{QS},micro_service_matched_wildcard_url=%{QS},micro_service_hostname=%{QS},configured_mitigation_action=%{QS},configured_mitigation_action_reason=%{QS},actual_mitigation_action=%{QS},actual_mitigation_action_reason=%{QS},browser_configured_verification_action=%{QS},browser_actual_verification_action=%{QS},browser_actual_verification_action_reason=%{QS},captcha_status=%{QS},browser_verification_status=%{QS},device_id_status=%{QS},device_id_action=%{QS},previous_initiated_action=%{QS},previous_initiated_action_status=%{QS},new_request_status=%{QS},enforced_by=%{QS},mobile_is_app=%{QS},challenge_failure_reason=%{QS},classification_reason=%{QS},client_type=%{QS},application_display_name=%{QS},application_version=%{QS},mobile_in_emulation_mode=%{QS},os_name=%{QS},jailbroken_or_rooted_device=%{QS},mobile_debugger_enabled_device=%{QS},imei=%{QS},human_behaviour=%{QS},http_request=%{QS}']
#
# }
kv {
field_split => ","
}
}
}
output {
elasticsearch {
hosts => ["https://mhqelastic-es-http:9200"]
index => "%{[@metadata][index]}"
user => "elastic"
password => "${ELASTICSEARCH_PASSWORD}"
ssl => true
cacert => "/var/data/tls.crt"
}
}